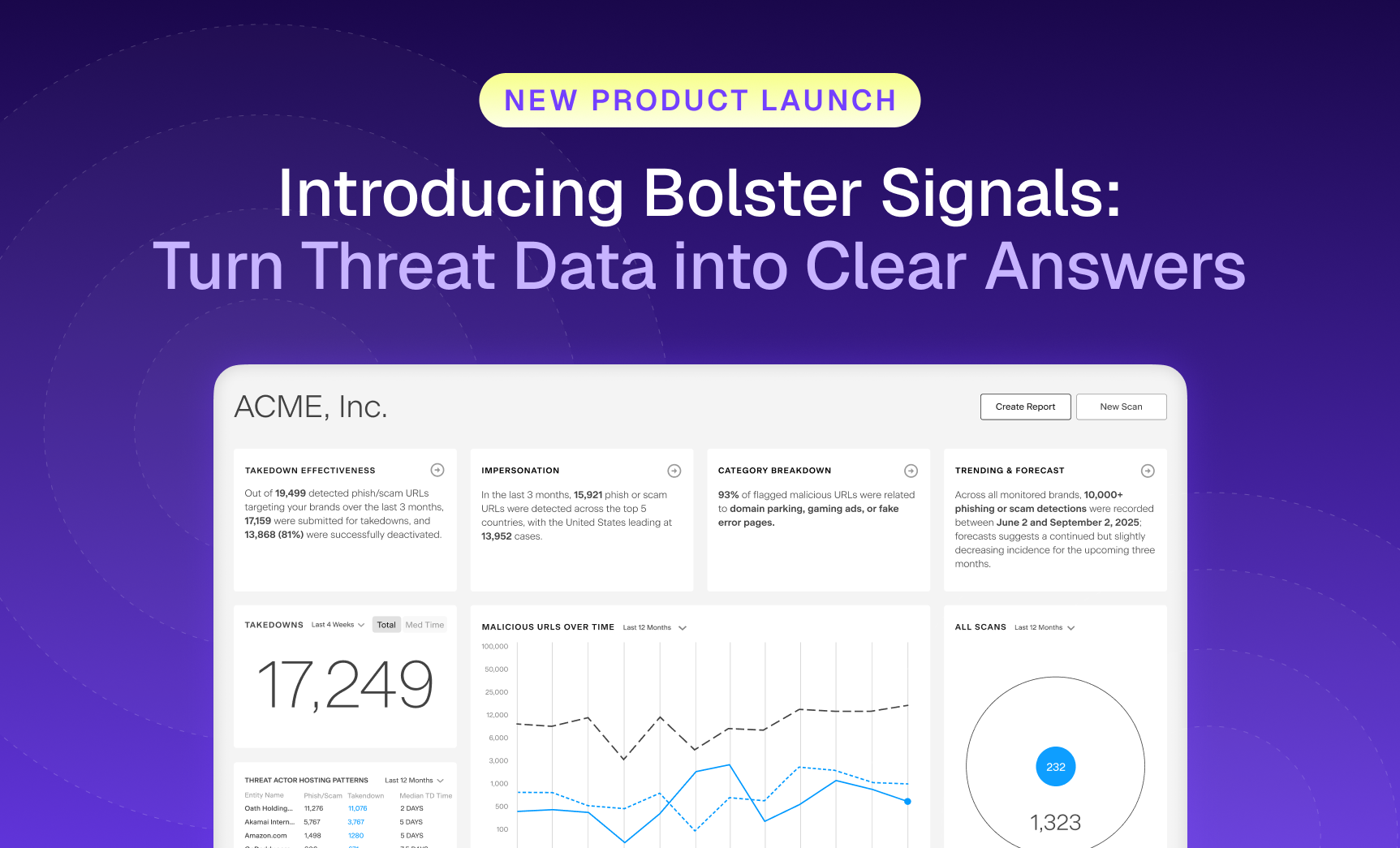
Security teams are flooded with more threat data than ever, and still struggle to see what matters most.…

The Bolster Blog
Thought provoking blogs discussing recent trends on digital risk protection services, phishing protection, threat intelligence, artificial intelligence, machine learning, brand protection and more!
Recent Posts
Allow Us to Reintroduce Ourselves: Meet the Customer Abuse Mailbox
Let’s clear something up. For a while, we referred to one of our most impactful features as “AI Security for Email.” While accurate in some.
Why AI-Generated Phishing Pages Are Harder to Detect (and How Bolster Stops Them)
Imagine clicking on what looks like your bank’s login page. The logo is crisp, the URL seems harmless at first glance, and even the support.

Buyer’s Guide: Purchasing a Brand Security Solution
Your brand is constantly under attack. To stay protected, you need an AI-powered brand security solution that keeps up with today’s AI-driven threats. Not sure what to look for? Use the Bolster AI Buyer’s Guide to evaluate your options.
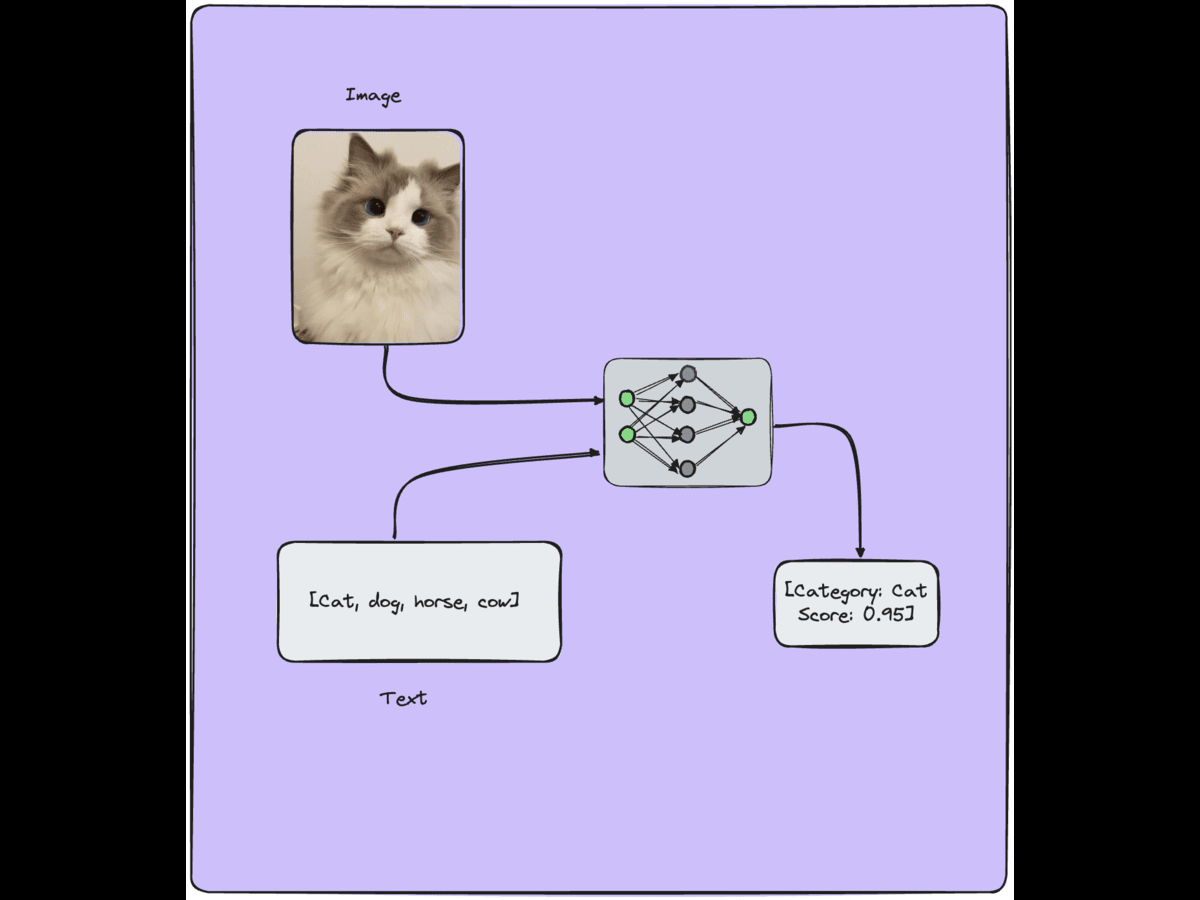
Vision Language Models Applications & Learning Strategies
Vision Language Models (VLMs) have applications in various fields, including…
The Need for AI Threat Detection in the Modern Cybersecurity Landscape
Today’s cybersecurity landscape demands much more than traditional threat detection,…
Telegram Phishing Bot Token Being Stolen from Scammers
At Bolster Research Labs, we recently observed that phishing kit…
Ad-ventures: Investigating the Misuse of Google Ads in Malvertising Campaigns
In the sprawling extent of the internet, Google Ads has…
Digital Risk Monitoring Importance is Growing Faster Than Ever
In a digital landscape that seems to be changing daily…
2024 State of Phishing & Online Scams: Statistics, Facts, Trends & Recommendations
From prompt responses to self-driving cars, 2023 felt the significant…
Announcing Bolster Community Forum
In the rapidly changing digital landscape, the cybersecurity community confronts…
Strengthening Singapore's Digital Defenses: A Deep Dive into Anti-Phishing Regulations
The rise in phishing attacks has become a global concern,…
Introducing Bolster’s Fully Customizable Table
Bolster, a leading provider of AI-powered phishing detection and response,…
Stealer Logs & The Threat That is Compromising Security
The arms race between cyber defenders and attackers is becoming…
Image Similarity for Brand Detection: A Comparison Between BEiT, SWIN and ViT-MAE
Image similarity has emerged as one of the most powerful…
Identifying Compromised Antivirus Software & Fake Sites
Antivirus vendors have significantly been impacted by the latest phishing…