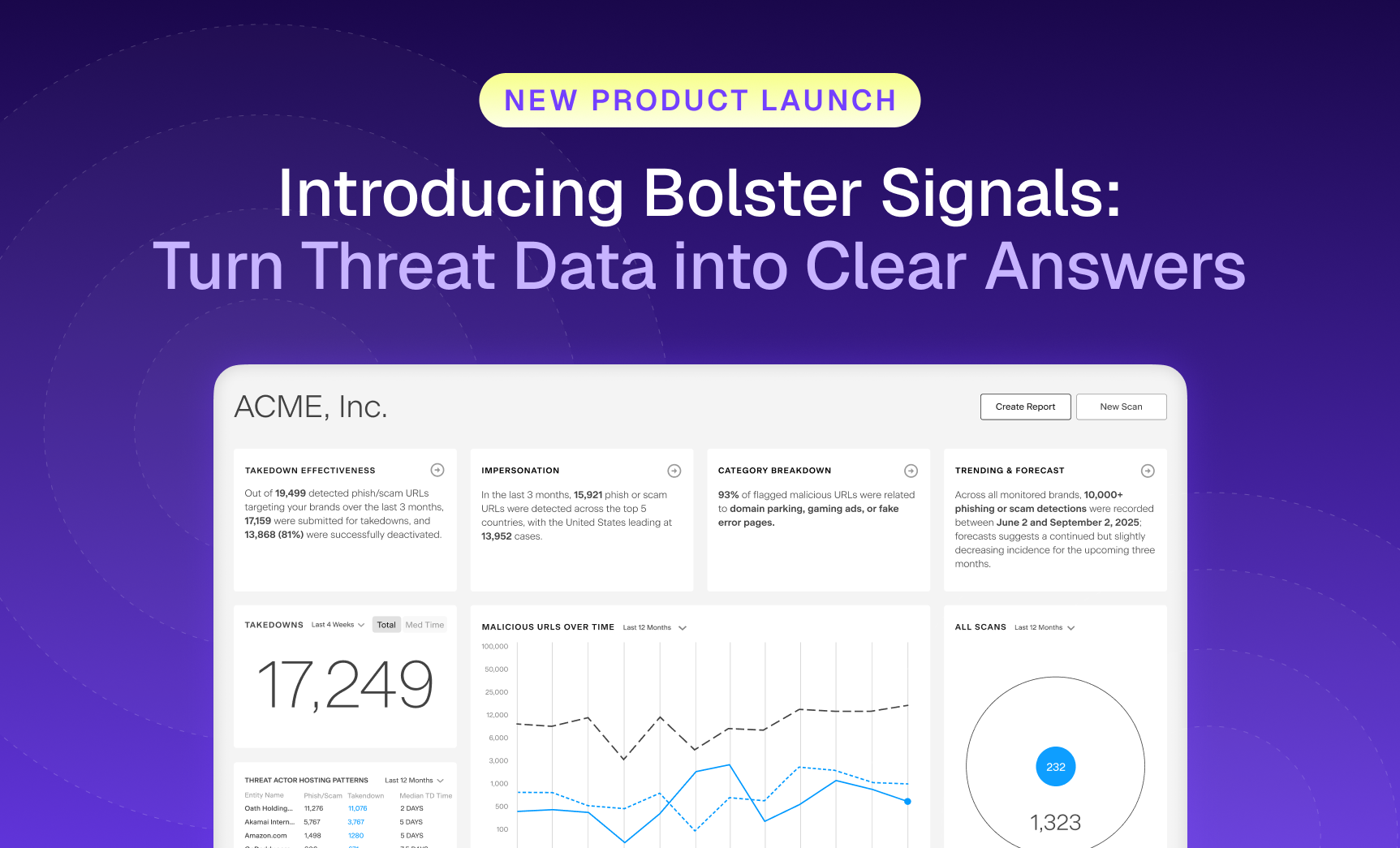
Security teams are flooded with more threat data than ever, and still struggle to see what matters most.…

The Bolster Blog
Thought provoking blogs discussing recent trends on digital risk protection services, phishing protection, threat intelligence, artificial intelligence, machine learning, brand protection and more!
Recent Posts
Allow Us to Reintroduce Ourselves: Meet the Customer Abuse Mailbox
Let’s clear something up. For a while, we referred to one of our most impactful features as “AI Security for Email.” While accurate in some.
Why AI-Generated Phishing Pages Are Harder to Detect (and How Bolster Stops Them)
Imagine clicking on what looks like your bank’s login page. The logo is crisp, the URL seems harmless at first glance, and even the support.

Buyer’s Guide: Purchasing a Brand Security Solution
Your brand is constantly under attack. To stay protected, you need an AI-powered brand security solution that keeps up with today’s AI-driven threats. Not sure what to look for? Use the Bolster AI Buyer’s Guide to evaluate your options.
What Are Executive Impersonation Attacks, and What Do They Look Like?
Cybercriminals keep coming up with new methods to deceive…
Top 4 Features of a Dark Web Monitoring Tool
The term “dark web” often gives off an ominous…
The Power of Automated Domain Monitoring
Today, business owners around the world understand that digital…
The 8 Most Common Anti-Phishing Solutions for Your Business to Utilize
Phishing is one of the primary threats to businesses…
The Importance of Automated Digital Risk Protection Services
Since the advent of the internet, digital risks have…
The Build vs. Buy Dilemma with Domain Risk Management
Domain risks are growing increasingly aggressive, and detrimental to businesses…
Evaluating Web Scraping, Crawling, and Automation with NodeJS Libraries
This blog is part 1 of a web scraping…
What’s Brand Protection Got to Do with External Attack Surface Management?
External attack surface management (EASM) encompasses a wide variety of…
Definitive Guide to Modern Brand Protection
Businesses are relying more and more on digital assets…
Account Takeover Fraud (ATO): 5 Steps for Protecting Your Customers
Account takeover fraud (ATO) is an attack where hackers compromise…
Phishing in the Metaverse: The New Reality of Brand Protection
The metaverse promises a new level of immersion and…
How Decentralized Web Hosting is Used in Phishing Campaigns
Decentralized web hosting moves away from reliance on centralized…